
Blog


How to Monitor a Small Production Server in 5 Minutes
How to Monitor Linux and MySQL Without Installing Heavy Software
Many monitoring platforms require installing multiple components, exporters, dashboards, and alert systems. But for small Linux and MySQL environments, there is a simpler approach that provides useful infrastructure insight without heavy monitoring stacks.

The Hidden Risk of Running Servers Without Health Monitoring
Small production systems rarely fail without warning. In most cases, problems build slowly through disk growth, memory pressure, rising load, slow queries, or MySQL connection stress. The risk is not just downtime. The real risk is not seeing the trend early enough to act.
Read More
Why Most Monitoring Tools Are Overkill for Small Infrastructure
Most monitoring platforms are built for large engineering teams managing hundreds of servers. But what if you run only a few Linux servers or a small MySQL environment? In many cases, enterprise monitoring tools introduce more complexity than value.
Add MCP server to claude code
MCP server extend functionality of the claude code
Read More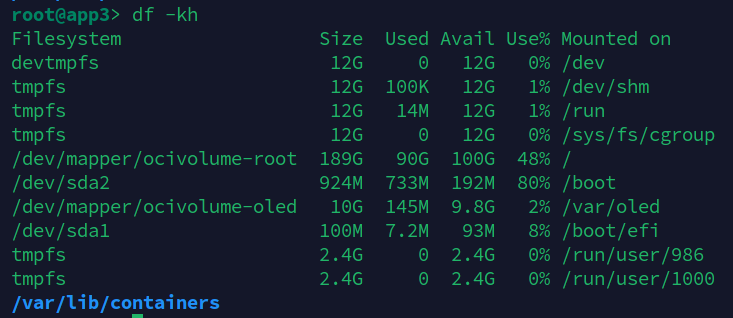
How to resize the boot drive in OCI
If you going out of space you have to to increase size of the partition. In this guide I explain step by step how to increase boot partition size on running server.
Read More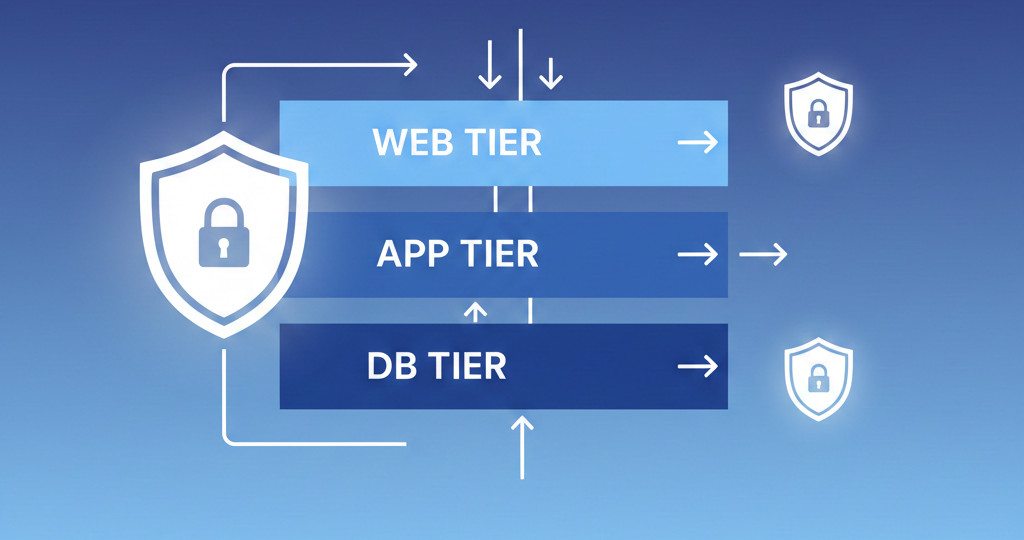
Designing a Multi-Tier Network in OCI: Best Practices and Implementation
In this guide, we'll design and build a classic three-tier architecture in OCI—web, application, and database layers. This is the setup used by nearly every enterprise workload because it provides scalability, separation of concerns, and strong security boundaries.
Read More
Securing Your OCI Network: Practical Best Practices for Every Deployment
In this guide, I’ll show you how to secure your Oracle Cloud network with the same approach I use in production customer environments. OCI offers enterprise-grade networking features—if configured properly. Security starts with the network. And in OCI, that means controlling access with VCNs, subnets, security lists, NSGs, IAM, gateways, and monitoring.
Read More