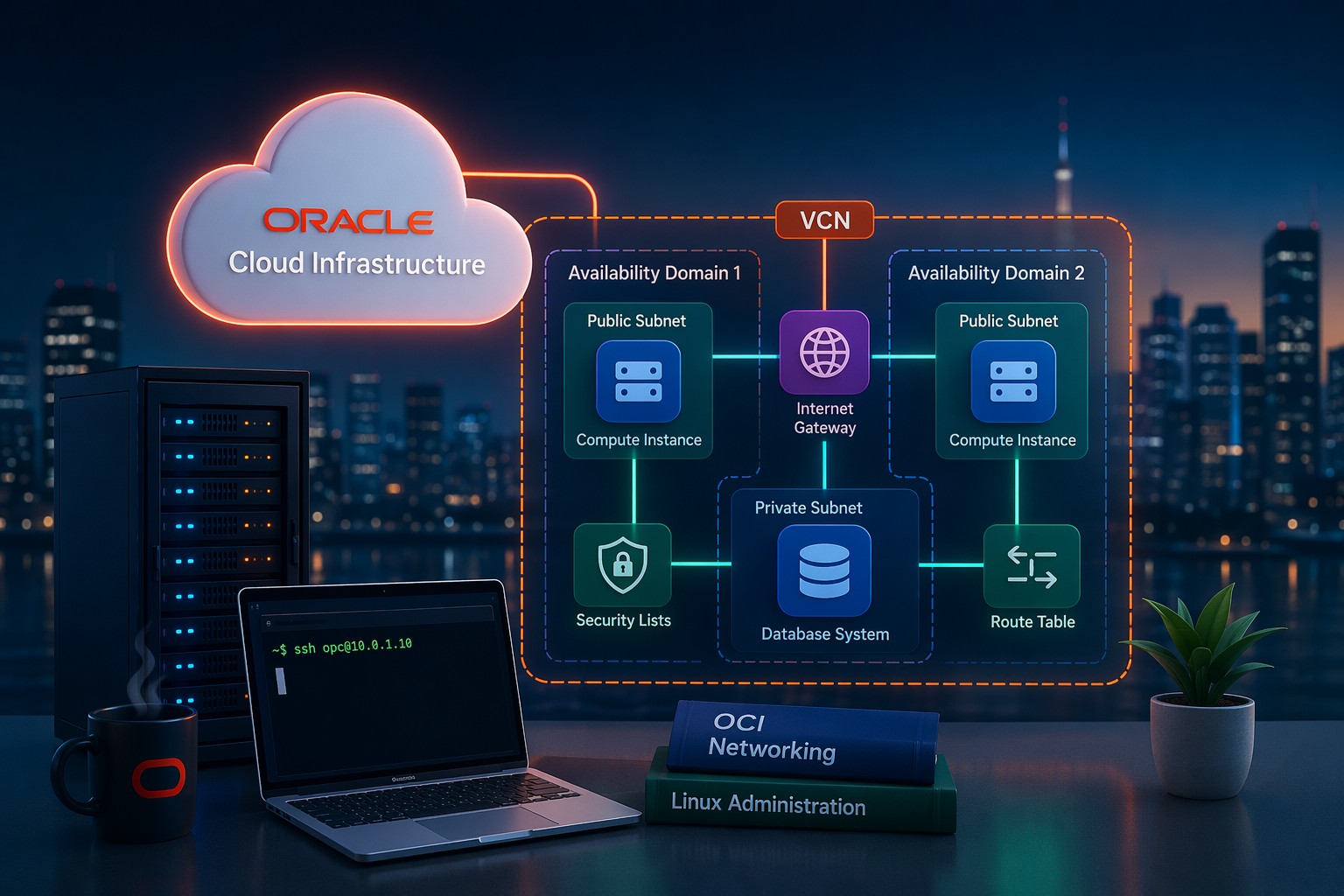
When you're building infrastructure in Oracle Cloud, one of the first security decisions you'll face is how to control traffic at the network level. And this is where many setups go wrong—not because of complexity, but because of confusion between Security Lists and Network Security Groups (NSGs).
They both act like firewalls. They both define ingress and egress rules. But they operate very differently in practice. Choosing the wrong one—or using them incorrectly—can leave your environment either exposed or unnecessarily complicated.
Let’s break this down in a way that actually helps you design better OCI networks.
Why This Distinction Matters
At a glance, Security Lists and NSGs look interchangeable. But in real deployments, the difference affects:
- How flexible your architecture is
- How easily you can scale or modify rules
- How clean your network design remains over time
- How well you can isolate workloads
Here’s the thing—if you rely only on Security Lists in a growing environment, you’ll quickly run into management headaches. On the other hand, if you misuse NSGs, you might overcomplicate simple setups.
What Are OCI Security Lists?
Security Lists are applied at the subnet level. That means every instance inside the subnet automatically inherits the same set of rules.
Key Characteristics
- Attached to subnets
- Applies to all VNICs in that subnet
- Acts as a basic network-wide firewall
This makes Security Lists simple and effective for small or uniform environments.
When Security Lists Work Best
- Simple architectures with similar instances
- Environments where all servers share the same access rules
- Early-stage deployments or test environments
But here’s the limitation: you lose granularity. You can’t easily define different rules for different instances in the same subnet.
What Are Network Security Groups (NSGs)?
NSGs operate at the instance (VNIC) level, not the subnet level. This gives you much finer control over traffic.
Key Characteristics
- Attached directly to VNICs
- Rules apply only to resources in the NSG
- Supports micro-segmentation
This is where OCI becomes much more flexible.
When NSGs Are the Better Choice
- Multi-tier applications (web, app, database layers)
- Environments requiring strict isolation
- Production systems with varying access needs
- Scalable architectures
Instead of relying on subnet boundaries, you define logical groupings of resources.
Security Lists vs NSGs: Side-by-Side
- Scope: Security Lists = Subnet | NSGs = VNIC level
- Flexibility: NSGs are more flexible
- Granularity: NSGs allow per-instance control
- Management: Security Lists are simpler, NSGs scale better
So what does this mean in practice?
Real-World Example
Imagine a typical 3-tier application:
- Web servers (public access)
- Application servers (internal only)
- Database servers (strictly restricted)
If you rely only on Security Lists, you’ll likely end up creating multiple subnets just to separate rules. That increases complexity quickly.
With NSGs, you can:
- Create one subnet
- Assign each tier to its own NSG
- Define rules between NSGs
This approach keeps your network design cleaner and more maintainable.
Common Mistakes to Avoid
1. Overusing Security Lists
This leads to rigid architectures that are hard to scale.
2. Mixing Too Many Responsibilities
Using both Security Lists and NSGs without clear intent creates confusion.
3. Ignoring NSGs in Production
NSGs are essential for modern, secure OCI deployments.
4. Poor Rule Documentation
Even well-designed rules become risky if no one understands them later.
Best Practice Approach
A practical strategy most teams follow:
- Use Security Lists for baseline subnet-level control
- Use NSGs for workload-specific rules
- Keep rules minimal and intentional
- Design around application architecture, not just networking
This gives you both structure and flexibility.
Summary
Security Lists and NSGs are not competing tools—they serve different roles. Security Lists give you a simple, subnet-wide control layer, while NSGs provide the precision needed for real-world applications.
If you're building anything beyond a basic setup, NSGs should be a core part of your design. They allow you to scale, secure, and manage your OCI environment without constantly redesigning your network.
And if you’re planning or refining your OCI infrastructure, taking the time to design network security properly will save you significant effort later. You can explore more practical OCI setup guidance and infrastructure design strategies at https://dmcloudarchitect.com/.